Residents of Turkmenistan who want to rent our servers for VPN often reach out to us. We have collected the most frequently asked questions and prepared detailed answers.
-
Facebook, Twitter, Instagram, YouTube, WhatsApp, Viber and Telegram messengers, and many other services are blocked in Turkmenistan. On top of that, individual IP addresses and entire subnets are blocked. Can I use your servers to set up a VPN for Turkmenistan?
We strongly discourage using our services to create a VPN on the territory of Turkmenistan! And here is why:
- according to our sources, IP addresses used for VPN in Turkmenistan are blocked within the first few days. Therefore, VPN services paid for on an hourly or daily basis are a better option to not waste money in vain. The minimum period for which you can rent our virtual servers is 1 month;
- we do not select IP addresses upon order of a VPS. The issued address may already be blocked in Turkmenistan. We cannot guarantee that the VPS you ordered will have an IP address that is not blocked in Turkmenistan;
- we do not perform a free or regular quick change of IP addresses on servers. Therefore, we recommend that you use services that specialize in providing VPN services.
-
If the IP address on my server is blocked, can you change it for free?
Sorry, but no. Blocking IP addresses in your country is not a reason for changing an IP address for free.
-
I want to pay to change the IP address. Is it easy to do?
You can purchase a new IP address, but you will have to change the IP address on your VPS. If you don't know how to do that, you will need to reinstall the operating system through the server control panel, but then all the data and server configuration will be deleted. To save them, you can contact us for a system administration service provided on a paid basis.
-
Is it possible to ping your IP addresses to find out if they are blocked or not?
We have a large IP pool for servers. However, no one can guarantee which address will be assigned to your server at the time of the order. This makes any testing pointless since it will not guarantee that the IP will be accessible from Turkmenistan.
-
Is it possible to check if the IP address is blocked or not?
Unfortunately, we do not have official block lists. Therefore, like any other hosting provider, we learn about the problem of blocking by the authorities of Turkmenistan only after users complain that the IP has stopped being available.
-
I ordered a VPS, but the IP address is already blocked. I paid for the change, but the new one is also blocked. Can all your addresses be blocked?
The more clients use our VPS to set up a VPN in Turkmenistan, and the more carelessly they do it, the more IP addresses are blocked and the more difficult it is to get an unblocked one.
Yes, you can store spare parts, tools, and accessories in a warehouse in our data center, if you have ordered colocation services or rack rental from us.
We will confirm the acceptance of the equipment that you bring to our data center, whether in person or delivery by any other source, by the act of acceptance and transfer. Opaque bags with components will be opened with your permission, in order to record the serial numbers and add them to the billing of the relevant customer ID. All equipment stored in the warehouse is marked with the customer ID to make it easier to identify and avoid loss.
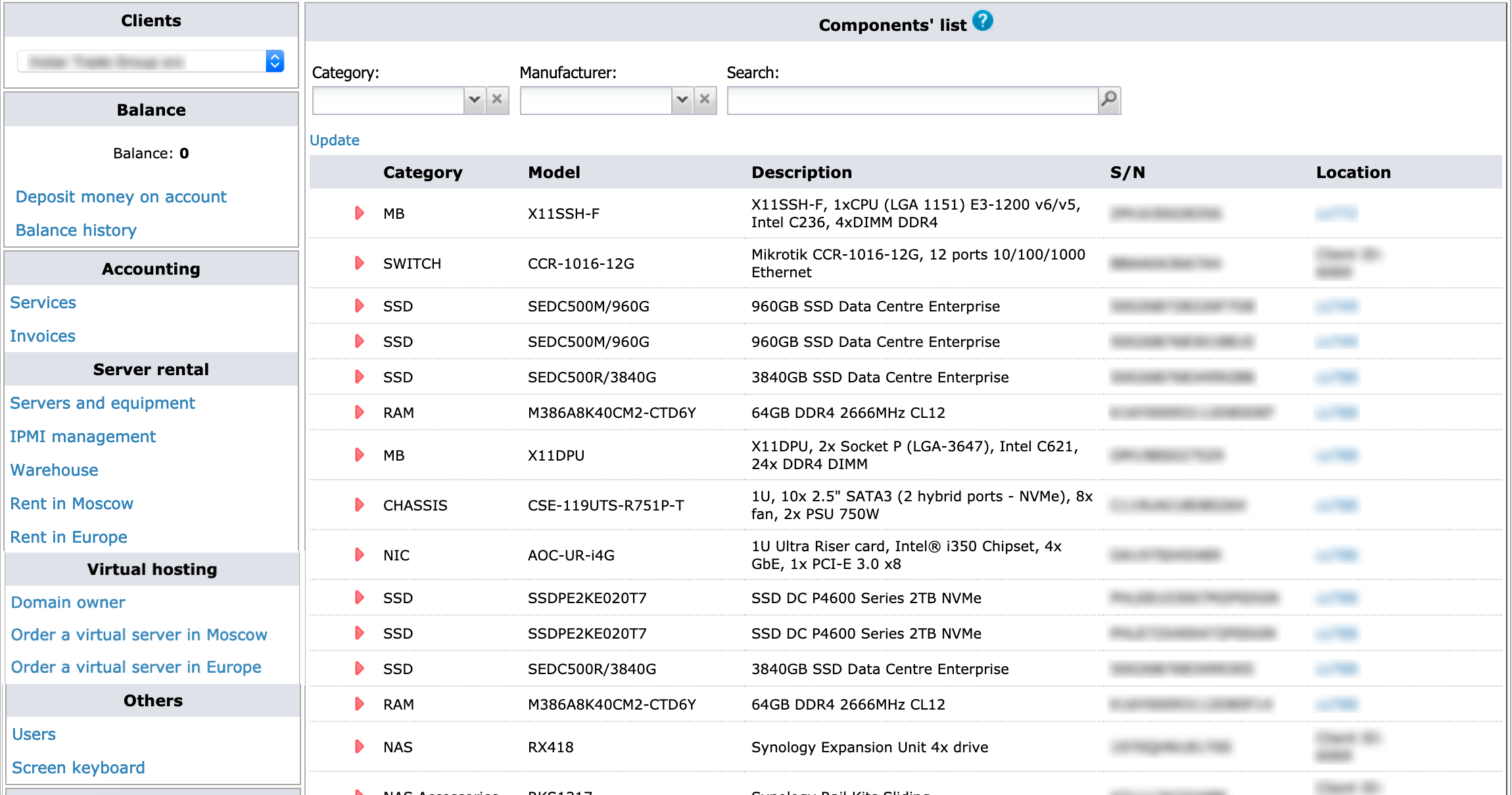
In your Personal Account, you can always view a list detailing your components, tools, and additional equipment stored in our warehouse or installed directly in your servers or racks.
DDoS protection is NOT included with any standard plan. It’s an additional paid service. The cost for anti-DDoS is individual and depends on many factors (because DDoS attacks are also unique).
Comprehensive DDoS protection may include a combination of the following: simple static traffic processing rules, sophisticated firewalling by special devices and/or self-learning systems, DNS solutions, geolocation load balancing and CDN, cooperation with backbone carriers, security companies and law enforcement agencies.
Unlike some other companies, we do not claim we provide a complete protection from any threat for free.
However, we have relevant experience and resources to mitigate entry- and mid-level DDoS attacks.
Sure, you can put a tamper-evident numbered seal on your rack. We can sign a formal note with a reference to the seal’s number. You get a hard copy of the note and we store another copy in the data-center.
Absolutely. You can provide your keys to us in person or ship it to the data-center. Our technicians will install it in your server free of charge.
If you need your keys back you can just get it in person in our office or we can ship it to you.
Our data-centers are operating all over the clock and authorized persons can visit it any time. Clients can use a dedicated room for equipment configuration and maintenance.
We do not verify if the apps you install are properly licensed.
However, we strictly recommend using only legal software to get critical updates and support in time and avoid copyright infringement claims.
You can rent software through us - it allows you to get a fully legitimate product and at the same time avoid significant investment.
You can also order additional services including OS installations and further OS and software maintenance by our professional engineering team.
You can find a complete list of all services in your Account.
Just check in in the list services you are going to renew and click on "Renew" button.
A new bill will be generated and you can then pay it using any available payment method.
Data-center security including your racks and equipment, is protected with electronic keys access control system, video surveillance and strictly followed policies.
On top of that, you can put a tamper evident numbered seal on your rack. We can sign a formal note with a reference to seal’s number. You get your hard copy of the note and we store another copy in the data-center.
If you order a server on a standard plan you will get all credentials (including IPs and IPMI access) on the same or next business day once we received the payment.
Standard servers (including ones on sale) are usually ready to use in 2 hours.
We can also prepare an individual server for you - it usually takes 3-7 days.
We offer plans that are a good balance between server capacity and uplink. It can be a specific amount of data or bandwidth available per month.
The following plans are available right now:
- unlimited data on 100 Mbit/s link - works for rack and dedicated server;
- 10Tb data on 1 Gbit/s link for a dedicated server;
- 20 Tb on 1 Gbit/s link or 10 Tb data on 10Gbit/s link for a rack.
We do not count european or international traffic. You should not maintain a specific rate of incoming/outgoing traffic.
If you’re on a limited plan - it means your incoming and outgoing traffic are summed up.
If you reached the limit - dont worry, we will not block or throttle you.
We will let you know beforehand that you’re approaching the limit. You’ll have time to decide - either to get more traffic or switch to an unlimited plan.
If you got unlimited plan - you have ‘all you can eat’ data limited only by your port speed.
We do not have any type of traffic limits, including shapers, FUP (fair usage policy) and network oversell.
Our ultimate goal is to grow together with our customers and hence we’re not interested in one-time tricks.
We have open peering policy and are seeking for the best connectivity.
Unfortunately, we cannt guarantee bandwidth in public Internet (between our datacenters and your endpoint). It’s just not possible because it depends on many different carriers.
In our internal network as well as between our data-centers, all traffic is free and unlimited.
Absolutely. We build complex high-load and reliable systems for our customers including e-commerce, financial institutions, search engines, TV channels and other media using online streaming.
It does not matter whether you plan to build your infrastructure from scratch or move the existing one into a new data-center. Lets get in touch and see how we can help you!